Despite growing awareness and preventive measures, malware attacks continue to compromise websites all across the globe. The overall cost of malware attacks has increased to $2 trillion and is expected to touch $6 trillion by the year 2021.
In recent years, hackers are designing and deploying more complex and sophisticated malware that can inflict more damage on websites – especially WordPress websites. Some of the common malware threats and hacks include:
- Pharma hacks, a sophisticated form of invisible hacking where hackers take advantage of your SEO practices to get your ranked pages to rank for their products – mostly banned drugs and prescription drugs. They do this by inserting SEO keywords into your website, creating malicious files/folders in your WordPress installation, or inserting suspicious links into text files.
- Backdoors, another covert form of attack where unauthorized users gain admin access to your account and corrupt your backend files with malicious or harmful code.
- SQL Injection, where malicious SQL code is inserted into data applications and is used to steal sensitive data from databases.
- Redirects, where legitimate site visitors are redirected to an unsolicited site where they end up downloading malicious files.
- Phishing, a form of a data breach where sensitive information like user credentials or credit card data, is obtained from users through deceptive websites or emails.
With all these types of malware threats, it’s important to be extra cautious when dealing with one on your business website. If your site is attacked by any of them, you may face some serious consequences, such as damaged search engine rankings. Unfortunately, when this happens, your site may experience a significant drop in web traffic and, in turn, lose many potential customers. To prevent these things from ruining your website and business as a whole, you need to familiarize yourself with how to find malware and address it right away.
But how are you supposed to do that? Read on to learn some of the best ways to search for hidden malware on your website.
Steps to Detect and Remove Malware
With so many different types of malware, how can you effectively detect hidden malware and avoid such attacks? You can do this by following these basic steps, carefully and thoroughly:
- Detect malware on your website.
- Clean the malware (manually or with a security plugin).
- Protect or harden your website to save it from future attacks.
Let’s look at each of these steps in more detail.
Step 1 – Detect any Malware on Your Website
The hard fact is – detecting a malware infection on your website can be tough. However, here are a few tell-tale signs that point towards a hacked website:
- Your site shows a sudden increase in loading time, or a drastic decrease in the incoming traffic.
- Your web host provider could intimate you of a possible malware infection. Alternatively, your website could be temporarily suspended by your web hosting company.
- Your website may no longer be appearing in the Google search results page, indicating that it could be blacklisted.
- Your incoming traffic is being redirected to an unsolicited or phishing website.
- Your website admin notes a large number of unknown plugins or users added to your account.
- Searching for your website on Google is displaying Japanese characters.
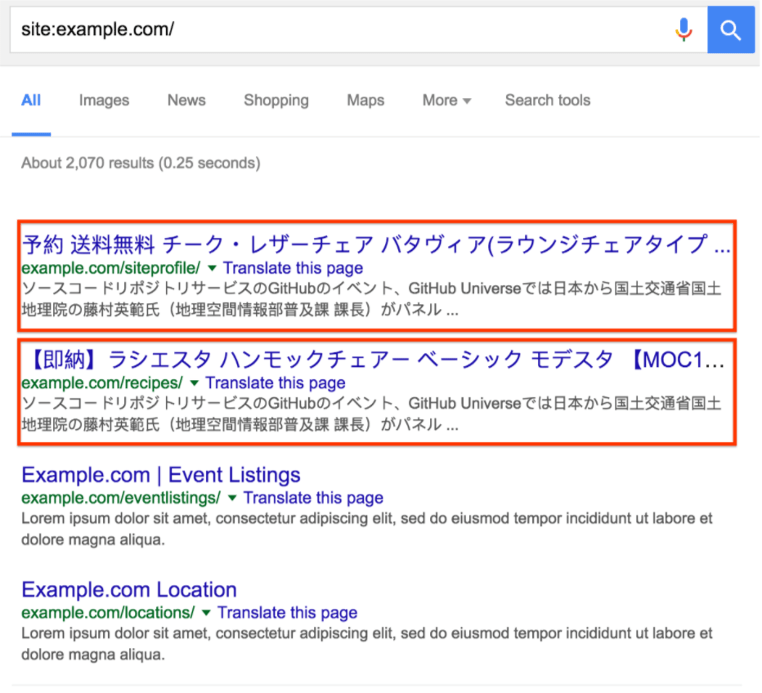
(Image Source: Google)
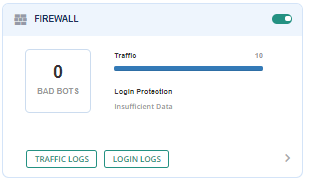
If you are witnessing any of these signs, do not waste any time and scan your website immediately. The easiest way to do this thoroughly is to use a WordPress security plugin like MalCare. With its deep scanning technology, its algorithm tracks every file change to detect the exact location of any malware.
To use this tool, you need to sign-up with MalCare and install using the MalCare dashboard. Once the plugin is installed, it automatically performs a complete scan of your website and reports if there are any malware infections.
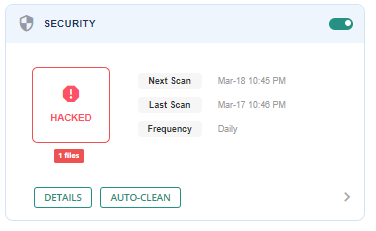
(Image Source: MalCare)
Step 2 – Clean the Malware from Your website
Once the malware has been detected on your website, you can proceed to remove it using either of the following methods:
Manual clean-up
Manual clean-up is only recommended if you possess the necessary technical expertise (and the additional time and energy) to do so.
In this process, you can either replace your infected website files with a fresh WordPress installation or with a backup copy of your website.
First, you need to manually clean up your infected website files as follows:
- Use an FTP tool like FileZilla to connect to your WordPress server files.
- Take note of all the recently modified files in your installation folder.
- Use the FTP tool to replace the modified files with a backup copy or a current version of WordPress.
- Manually edit any customized WP files to remove any malware code.
Next, you need to manually clean up your infected WordPress database tables as follows:
- Sign in your WordPress database panel from your web hosting account.
- Scan manually for any spam keywords or suspicious links in your database tables.
- Delete the database records containing malicious entries from the respective tables.
Among its limitations, manual clean-ups are not effective in detecting and removing website backdoors as smart hackers embed backdoor code into files (that are named similar to standard WP files) or into PHP functions like Base64 and Eval. Besides that, they use different keywords that cannot be detected manually.
Automatic clean-up using security plugins
Comparatively, automatic clean-ups using WordPress malware removal plugins are more effective in detecting and removing various types of malware infections. Here are the top three WP security plugins available in the market:
- MalCare: Easy to install and use, the MalCare plugin enables you to clean your hacked website in a matter of minutes. At just $99 a year, you can avail of unlimited malware removal and automatic daily malware scans to keep your site safe.
(Image Source: MalCare)
- Sucuri: The Sucuri tool is also efficient in removing malware infections, repairing SEO spam, and preventing future attacks. The Basic plan is priced at $199.99 yearly.

(Image Source: Sucuri)
- Wordfence: Wordfence is another popular security plugin that provides complete cleaning services for a single website for $179 a year.

(Image Source: Wordfence)
Besides these, CleanMyMac X is an excellent malware removal tool you can consider using, especially if you are developing a WordPress site on your Mac. Despite Apple’s best efforts, new malware threats are looming over the heads of Mac users, even with the new M1 chips. So whether you are suddenly losing RAM or your device is running slower than before, installing this malware tool will ensure you can focus solely on your project. Ensure to run this software in the background, and don’t forget to scan your system regularly. Thanks to the Smart Scan feature of this tool, you’ll get a quick overview of your system’s health.
Indeed, there are many methods to consider when removing hidden malware from your website. Although these procedures are important for your reference, it may still be an excellent idea to consult a ransomware removal service to clear your systems of these cybersecurity threats and other viruses.
Given the huge impact of malware on your site when undetected, seeking assistance from professionals specializing in malware removal proves to be beneficial. They have the necessary skills, experience, and expertise that can help them clean malware from your website successfully. Not only that but they can also implement an effective cybersecurity strategy to prevent future cyberattacks from damaging your website again.
Step 3 – Protect or Harden Your Website from Future Attacks
After a complete website clean-up, the next step is to protect or harden your site from any future attacks. While there is no such thing as 100% protection from malware attacks, performing the following steps can improve your site security:
- Configure your security plugins like MalCare or Sucuri to periodically scan your complete website for new infections. Additionally, use firewall protection to block requests from suspicious IP addresses.
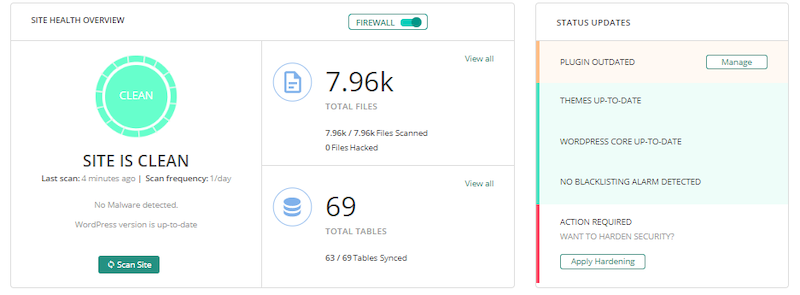
(Image Source: MalCare)
- Do not run your website on an outdated WordPress version or outdated plugins/themes. Update your WordPress to the latest released version along with all your installed plugins/themes. As a precautionary measure, take regular backups of your website files and database tables. To make things easy, install WordPress backup plugins like BlogVault.
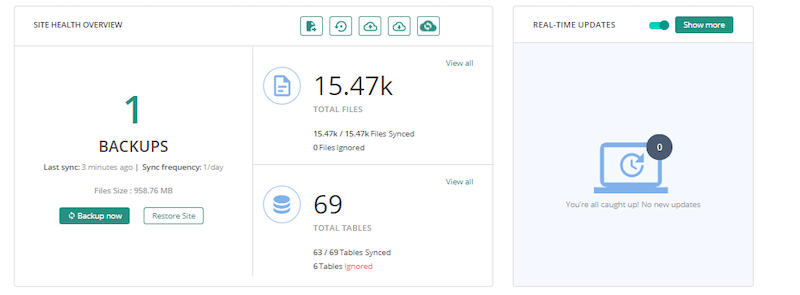
(Image Source: BlogVault)
- If your website is currently hosted on a shared host, it’s a good time to switch to the more secure managed hosting offerings. Also, check with your current hosting company on the security features that they are offering.
- Download and install plugins/themes only from trusted sources like the WordPress repository, trusted WordPress marketplaces, or from known plugin/theme developers or companies.
- Prevent brute force attacks in the future by strengthening your WordPress user credentials. This includes the mandatory use of 8-character passwords (including lowercase and uppercase characters, alphanumeric characters, and special characters) and the use of unique usernames for each user.
- Get your website SSL-certified that ensures encryption of data transferred between your web server and the user’s browser.

- Make use of a plugin like WP Security Audit Log that monitors real-time user activity on your website.
Conclusion
Cyberattacks are a reality of today’s connected world. While there is no 100% guaranteed security against hackers, you can do your best to improve your site security and make it that much harder for hackers. The measures outlined in this article are a great place to start. Security plugins like MalCare and Sucuri rely on their research and experience in WordPress security to design evolving and comprehensive malware detection and removal strategies. We highly recommend that you invest in a security plugin that meets your needs and fits your budget.
What do you think of these security measures? How else can you safeguard your website? Do share your thoughts and recommendations in the comments section below. We would love to hear from you.

Great job indeed, One of the most precious posts on the topic of malware attacking in the WordPress site. I have suffered many times from this kind of attack and I have known about how painful is it to recover if you got attacked or hacked. So if you want to safe from this, you have to aware of it and I think this article will help you a lot in this issue.